Refresh tokens
Refresh tokens enable granting long-term access to APIs. You should keep the lifetime of access tokens as short as possible. However, you want to avoid forcing the user to perform repeated front-channel round trips to the authentication server to request new access tokens.
Refresh tokens allow new access tokens to be requested without user interaction. Every time the client refreshes a token, it needs to make an authenticated back-channel call to the authentication server. This call allows verifying if the refresh token is still valid or has been revoked.
Refresh tokens are supported in the authorization code and resource owner password flows. To request a refresh token, the client must include the offline_access scope in the token request and must be authorized for that scope.
Refresh tokens expire after 30 days. Refresh tokens have a sliding lifetime window of 15 days. The lifetime of a refresh token is renewed by the amount of time specified in the SlidingRefreshTokenLifetime parameter. After 30 days, the client must reauthenticate, regardless of the validity period of the most recent refresh token acquired by the application.
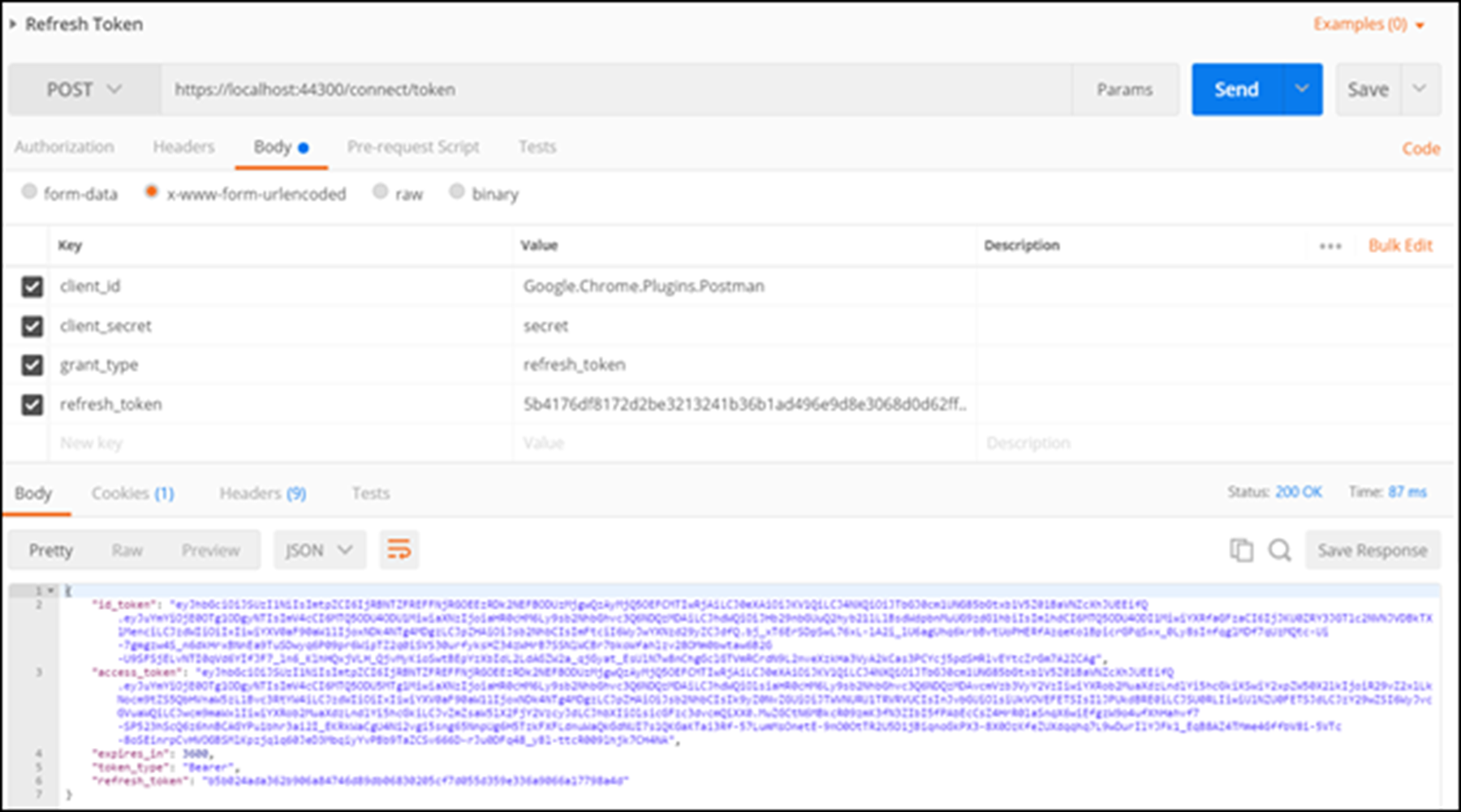
To obtain a new access token from a refresh token, send the following information:
URL
: https://<server>/AuthServices/Auth/connect/tokenHTTP Verb
: POSTParameters:
- client_id<client_id>
- client_secret: <secret>
- grant_type: refresh_token
- refresh_token: <current valid refresh token>
The following is a Postman request and response for the refresh_token grant: